Access List
Question 1
Explanation
The first answer is not correct because the 10.0.0.0 network range is not correct. It should be 10.0.0.0. to 10.255.255.255.
Question 2
Explanation
Logging-enabled access control lists (ACLs) provide insight into traffic as it traverses the network or is dropped by network devices. Unfortunately, ACL logging can be CPU intensive and can negatively affect other functions of the network device. There are two primary factors that contribute to the CPU load increase from ACL logging: process switching of packets that match log-enabled access control entries (ACEs) and the generation and transmission of log messages.
Process switching is the slowest switching methods (compared to fast switching and Cisco Express Forwarding) because it must find a destination in the routing table. Process switching must also construct a new Layer 2 frame header for every packet. With process switching, when a packet comes in, the scheduler calls a process that examines the routing table, determines which interface the packet should be switched to and then switches the packet. The problem is, this happens for the every packet.
Reference: http://www.cisco.com/web/about/security/intelligence/acl-logging.html
Question 3
Explanation
If you use the “debug ip packet” command on a production router, you can bring it down since it generates an output for every packet and the output can be extensive. The best way to limit the output of debug ip packet is to create an access-list that linked to the debug. Only packets that match the access-list criteria will be subject to debug ip packet. For example, this is how to monitor traffic from 1.1.1.1 to 2.2.2.2
| access-list 100 permit ip 1.1.1.1 2.2.2.2 debug ip packet 100 |
Note: The “debug ip packet” command is used to monitor packets that are processed by the routers routing engine and are not fast switched.
Question 4
Question 5
Question 6
Explanation
+ The question asks to “always” block traffic (every week) so we must use keyword “periodic”.
+ Traffic should be blocked to 11:59 PM, which means 23:59
Note: The time is specified in 24-hour time (hh:mm), where the hours range from 0 to 23 and the minutes range from 0 to 59
Only answer B satisfies these two requirements so it is the best answer. In fact, all the above answers are not correct as the access-list should deny web traffic, not allow them as shown in the answers.
Question 7
Question 8
Question 9
Explanation
The established keyword is only applicable to TCP access list entries to match TCP segments that have the ACK and/or RST control bit set (regardless of the source and destination ports), which assumes that a TCP connection has already been established in one direction only. Let’s see an example below:
 Suppose you only want to allow the hosts inside your company to telnet to an outside server but not vice versa, you can simply use an “established” access-list like this:
Suppose you only want to allow the hosts inside your company to telnet to an outside server but not vice versa, you can simply use an “established” access-list like this:
| access-list 100 permit tcp any any established access-list 101 permit tcp any any eq telnet ! interface S0/0 ip access-group 100 in ip access-group 101 out |
Note:
Suppose host A wants to start communicating with host B using TCP. Before they can send real data, a three-way handshake must be established first. Let’s see how this process takes place:
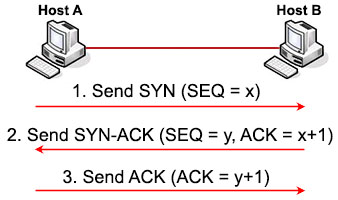
1. First host A will send a SYN message (a TCP segment with SYN flag set to 1, SYN is short for SYNchronize) to indicate it wants to setup a connection with host B. This message includes a sequence (SEQ) number for tracking purpose. This sequence number can be any 32-bit number (range from 0 to 232) so we use “x” to represent it.
2. After receiving SYN message from host A, host B replies with SYN-ACK message (some books may call it “SYN/ACK” or “SYN, ACK” message. ACK is short for ACKnowledge). This message includes a SYN sequence number and an ACK number:
+ SYN sequence number (let’s called it “y”) is a random number and does not have any relationship with Host A’s SYN SEQ number.
+ ACK number is the next number of Host A’s SYN sequence number it received, so we represent it with “x+1”. It means “I received your part. Now send me the next part (x + 1)”.
The SYN-ACK message indicates host B accepts to talk to host A (via ACK part). And ask if host A still wants to talk to it as well (via SYN part).
3. After Host A received the SYN-ACK message from host B, it sends an ACK message with ACK number “y+1” to host B. This confirms host A still wants to talk to host B.
Question 10
Explanation
Reflexive access lists provide filtering on upper-layer IP protocol sessions. They contain temporary entries that are automatically created when a new IP session begins. They are nested within extended, named IP access lists that are applied to an interface. Reflexive access lists are typically configured on border routers, which pass traffic between an internal and external network. These are often firewall routers. Reflexive access lists do not end with an implicit deny statement because they are nested within an access list and the subsequent statements need to be examined.
Reference: http://www.cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-1s/sec-access-list-ov.html
Question 11
Explanation
The command “ipv6 traffic-filter access-list-name { in | out }” applies the access list to incoming or outgoing traffic on the interface.
Question 12
Question 13
Explanation
When the ACL logging feature is configured, the system monitors ACL flows and logs dropped packets and statistics for each flow that matches the deny conditions of the ACL entry.
The log and log-input options apply to an individual ACE and cause packets that match the ACE to be logged. The sample below illustrates the initial message and periodic updates sent by an IOS device with a default configuration using the log ACE option.
*May 1 22:12:13.243: %SEC-6-IPACCESSLOGP: list ACL-IPv4-E0/0-IN permitted tcp 192.168.1.3(1024) -> 192.168.2.1(22), 1 packet
Reference: https://www.cisco.com/c/en/us/about/security-center/access-control-list-logging.html
From the example above we can see when an ACL drops a packet, it generates a level 6 Syslog (%SEC-6-)



can some one tell me that where are the questions of these explanations?
jilla tamil mp3 – myfreemp3.review/search/jilla-tamil-mp3/
download free music
Download 41q + 150q PDF
vce exam file
vce cracked version
adf#.ly/#1i60JQ
(Remove # and go to the link to download)
dumps on kunal18oct(AT)gmail.co,
dumps on kunal18oct(AT)gmail.com
please send me the latest valid dump to dchaps @ yahoo dot com have date this saturday.
please send me the latest valid dump to dchaps_kevin @ yahoo dot com have date this saturday.
please send me the latest valid dump to {email not allowed} have date this saturday.
guys it looks like the exam has changed any updates
@Anonymous
I think we’re starting to get some positive feedbacks under “share your experience” page……
please send me the latest valid dump to revladimir @ mail . ru
can somebody tell me please that what is the last question of 40Q of TAGWA , in my life there is no answer of question “Meaning of priority 0 configured in ospf router?” .
can somebody tell me please that what is the last question of 40Q of TAGWA , in my life there is no answer of question “Meaning of priority 0 configured in ospf router?” . Plus what it the correct answer for the following questions?
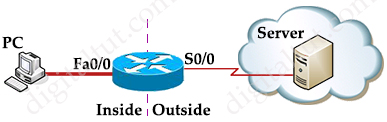
Question 2
Refer to the following configuration command.
router(config)# ip nat inside source static tcp 172.16.10.8 8080 172.16.10.8 80
Which statement about the command is true?
A. Any packet that is received in the inside interface with a source IP port address of
172.16.10.8:80 is translated to 172.16.10.8:8080.
B. Any packet that is received in the inside interface with a source IP port address of
172.16.10.8:8080 is translated to 172.16.10.8:80.
C. The router accepts only a TCP connection from port 8080 and port 80 on IP address
172.16.10.8.
D. Any packet that is received in the inside interface with a source IP address of 172.16.10.8
is redirected to port 8080 or port 80.
Answer:?
and
Question 28
A network engineer wants to ensure an optimal end-to-end delay bandwidth product. The delay is
less than 64 KB. Which TCP feature ensures steady state throughput?
A. Window scaling
B. Network buffers
C. Round-trip timers
D. TCP acknowledgments
Answer:?
some people said the answer is wrong of TAGWA file. Please help
you want NAT to redirect packets from the outside destined for 172.16.10.8:80 to
172.16.10.8:8080. You can use a
static nat
command in order to translate the TCP port number
to achieve this. A sample configuration is shown here.
Configuring NAT to Redirect TCP Traffic to Another TCP Port or Address
Note that the configuration description for the static NAT command indicates any packet received
in the inside interface with a source address of 172.16.10.8:8080 is translated to 172.16.10.8:80.
This also implies that any packet received on the outside interface with a destination address of
172.16.10.8:80 has the destination translated to 172.16.10.8:8080.
The final step is to verify that NAT is operating as intended.
show ip nat translations
Pro Inside global Inside local Outside local Outside global
tcp 172.16.10.8:80 172.16.10.8:8080 — —
Example: Using NAT During a Network Transition
Deploying NAT is useful when you need to readdress devices on the network or when you replace
one device with another. For instance, if all devices in the network use a particular server and this
NAT Router
interface ethernet 0
ip address 172.16.10.1 255.255.255.0
ip nat inside
!— Defines Ethernet 0 with an IP address and as a NAT
inside interface.
interface serial 0 ip address
200.200.200.5 255.255.255.252 ip nat outside
!—
Defines serial 0 with an IP address and as a NAT outside
interface.
ip nat inside source static tcp 172.16.10.8
8080 172.16.10.8 80
!— Static NAT command that states
any packet received in the inside !— interface with a
source IP address of 172.16.10.8:8080 is !— translated
to 172.16.1
http://www.cisco.com/c/en/us/support/docs/ip/network-address-translation-nat/13772-12.pdf
Jane, ospf priority only comes into play when you’re talking a broadcast network (think Ethernet). In this case, a DR and BDR are elected. To be able to participate in the election process, the ospf priority on an interface must be 1 or greater. If it’s set to 0, it will not participate in this election process.
Can someone explain why answer D (and not A) is correction for question 4?
who have got latest 300-101 dump pls send to azecisconetwork at gmail.com
Abu February 6th, 2017
anyone have 300-101 up to date dumps, I have 300-115 up to date dumps. we can exchange. email me ayousufzai at gmail.com
At this link it said: “If you enable CEF and then create an access list that uses the log keyword, the packets that match the access list are not CEF switched. They are fast switched. Logging disables CEF.”
http://www.cisco.com/c/en/us/td/docs/ios/12_2/switch/configuration/guide/fswtch_c/xcfcef.html#wp1000943
I’m confused…What is correct?
En la parte menos pública accesible de la web
donde se transan secretos industriales y póliticos y se comercia con todo género de recursos y commodities, muchos de ellos ilegales. http://www.braintuitions.com/index.php/component/k2/itemlist/user/611209
This info is priceless. How can I find out more?|
http://www.JpJpknRtUM.com/JpJpknRtUM
SOS,Someone,please send latest dumbs to sigm3618@gmail dot com
I found part of the questions here https://drive.google.com/open?id=0B5mAFqgydmCzTGd0VU9nQVZEaEE
Could you please send me the latest dumps of CCNP Route (300-101)!!! {email not allowed}
please someone email me the newest dump narcisse.aspilaire at gmail thank you in advance, anything that would help greatly appreciated
Why are the questions not displayed ?
Hi All,
Kindly let me know is there any change in syllabus?
What is the display output of command Ip Cache flow? Please answer important for CCNP Route exam ?
Everything you need to pass the exam.
Thank you friends of digital.tut.
Compilation of exams and including April and May.
http://microify.com/1pFk
the pass is
!aAyefgyn-7nP18rSvGvzPPv5FJbO_e8AmeieWSZZtTk
Hi logipy
Some of your responses are not correct, please update them
Hello anyone, can you help me with the dumps Route and TSHOOT?
My e-mail is: info AT anemosradio.com
Thank you!
Hi,
Can anyone please share latest dump of 300-101 Routing at {email not allowed}.
Thanks
Hey can anyone provide some information about any valid CCNP Route dumps please. I saw this post by @logipy and wanted to know which dumps to follow and if the 9tut dumps are also valid or not?
Thanks in advance.
Recently, anyone passed CCNP-route exam? anyone have latest valid dumps?
anyone passed CCNP-route exam? anyone have latest valid dumps?
send me at {email not allowed}
@anonymous
plz i sent to you…. plz replay
Hi logipy,
Thank you! Are these dumps from April-May still valid?
Hi memo,
Got a reply from Anonymous fro the latest dumps?
anyone passed CCNP-route exam? anyone have latest valid dumps? and PDF Questions and answers.
Please send it to me ( {email not allowed})
403Q… IS IT VALID?
What’s up with Q 7 in “Access List” section? Is it not complete?
please send me the latest version of dump file
I do the exam next month
sara.faruq21 (a)gmail
thanks
Can you please send the dumps. I’ve my exam next month
{email not allowed}
Are all the answers correct here?
ACL is very important guys..be carefull on the exam…
here is a review with PT example
http://ipcisco.com/standard-acl-configuration-with-packet-tracer/
Hello Guys,
Could some help me by mailing the latest dumps for 300-101 exam.
Regards,
Phanindra Ponnada.
Failed today with 760pts….although I cleared all my labs , loads of new questions ,don’t trust any dumps…study hard chaps….and loads of simlet ( IPV6 , ACL, NAT, NAT-PT ETC ETC )
ACL very important ( IPV6 and IPV4 both)
For latest valid dump with continuous update, please contact me at steffyshirls @ gmail .com
Hello guys,
Im looking for CCNP latest Routing and switching Dumps. If possible can you pls send it to {email not allowed}
Thanks in Advance.
Naveen kumar
Hio guys, can you send the latest valid dump
Can someone help with latest dumps? ogunseyemoses at gmail