Embedded Event Manager (EEM) Tutorial
EEM (Embedded Event Manager) is a software component of Cisco that allows network administrators to automate many tasks. EEM is like a programming language with “if {condition} then {action}” statement. If your condition is met then some “actions” will be performed automatically on the device.
An EEM consists of two major components:
+ Event: Defines the event to be monitored
+ Action: Defines action to be taken when the event is triggered
There are three steps to creating an EEM applet.
Step 1. Create the applet and give it a name with the command “event manager applet applet-name“
Step 2 (Optional). Tell the applet what to look out for (just optional as some applets do not need to look out anything), usually with “event cli pattern” command
Step 3. Define action to be taken when the event is triggered in step 2, usually with “action” or “set” command.
Note:
+ The event commands are used to specify the event criteria that trigger the applet to run
+ The action commands are used to specify an action to perform when the EEM applet is triggered
+ The set command is used to set the value of an EEM applet variable
It is easier to learn about EEM via examples so let’s start with some simple ones:
| Note: These commands were tested with Cisco IOS v15.4(1)T. Some keywords may not be available in older versions. |
Example 1
Show a welcome message with “show my welcome” command. Of course there is no valid “show my welcome” command on Cisco routers by default and you will get an error when using it. But we will configure EEM to output a welcome message with this command.
Required commands:
! event manager applet SHOW-MY-WELCOME-COMMAND event cli pattern "show my welcome" enter action 1 puts "Hello!!! Welcome to digitaltut.com!!!" !
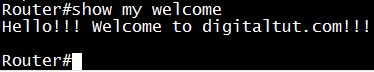
Output
Explanation for above commands
+ The “event manager applet SHOW-MY-WELCOME-COMMAND” defines name of our applet, which is “SHOW-MY-WELCOME-COMMAND”
+ The “event cli pattern” command will catch any command which is issued to our VTY terminal. If the written command is “show my welcome” then our condition is met and our action in the next line will be triggered. The keyword “enter” here means “Event match upon Enter key”
+ The “puts” actions writes a string to the active terminal
Note:
+ Our EEM will match “show my welcome” command in any mode (even in global configuration or VTY mode):
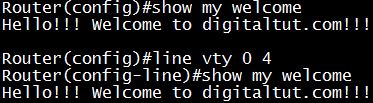
We can limit our command in exec mode only with the command event cli pattern “show my welcome” mode exec enter.
+ If the written command includes the text “show my welcome” (for example we can enter command “KKSKSshow my welcomeFDFK”) then our message will be printed out:
![]()
It is sometimes dangerous and uncontrollable. If we want to show our welcome message with the exact “show my welcome” command only then we can use Regular Expression in our event. Our command should be event cli pattern “^show my welcome$” enter). “^” and “$” are symbols in Regular Expression, which means “Start of a string” and “End of a string”, respectively.
-> The perfect event command should be event cli pattern “^show my welcome$” mode exec enter
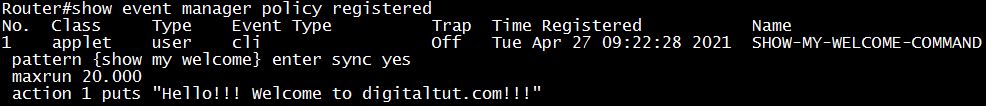
We can verify our registered EEM applet via the “show event manager policy registered” command:
Example 2
Let’s create a manually triggerd EEM applet which show a syslog message once we run it:
Required commands:
! event manager applet Welcome_to_digitaltut event none action 1 syslog msg "Welcome to digitaltut!!!" !
Explanation for above commands
+ In this example, we do not have a matching pattern as it is just simply print a welcome message on the terminal.
+ The “event none” does not allow the script to run automatically. It allows manual execution of the script from a CLI command using “event manager run <script-name>”
+ The “syslog msg” action allows displaying a syslog message. It is useful when we monitor remote devices via a Syslog server.
+ “action 1” is just the number of an action.
Output
Router#event manager run Welcome_to_digitaltut
Router# *Apr 27 07:26:39.551: %HA_EM-6-LOG: Welcome_to_digitaltut: Welcome to digitaltut!!!
Example 3
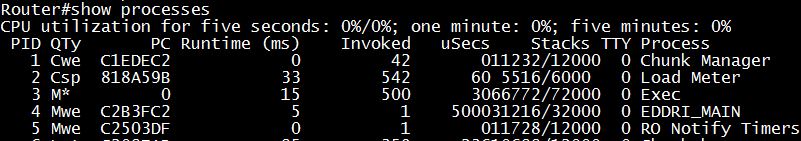
Block the output of command “show processes”. Also send a Syslog with the priority of “Critical” to the Syslog server.
By default we will see a long list of processes running on our router with this command :
Now we will use EEM to block this command.
Required commands:
! event manager applet BLOCK-SHOW-PROCESSES-COMMAND event cli pattern "show proc" sync yes action 1 syslog priority critical msg "Syslog message: show processes command entered" action 2 puts "This command is blocked!" action 3 set _exit_status "0" !
Output
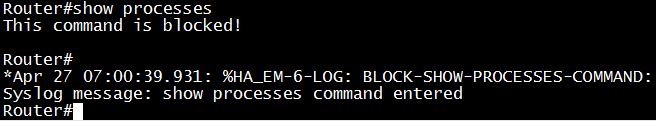
Explanation for above commands
+ We should block the short form “show proc” so that it can block all “show process”, “show processes”, “do show processes” commands. We cannot block shorter command “show pro” because it will also block “show protocols” command. We should not use “^show proc” pattern because someone can bypass it via the “do show proc” command.
+ We need “sync yes” keyword here because our EEM applet must run before the CLI command is executed so that EEM can block the execution of this command (via _exit_status in action 3). Without “sync yes” keyword, our EEM would run in parallel with the CLI command so we cannot block it.
+ The “syslog priority critical” set the priority of Syslog message to “Critical”
+ Set the “_exit_status” variable to “0” would block the executed command (“1” would allow the original command to run after script execution)
+ If you want to insert another action between action 2 and action 3, you can use “action 2.1”, “action 2.2″…
Example 4
Use an EEM applet to create a single line command to perform “clear counters” hiding the [confirm] prompt
Required commands:
! event manager applet CLEAR-COUNTERS event none action 1 cli command "enable" action 2 cli command "clear counters" pattern "\[confirm\]" action 3 cli command "y" ! alias exec cc event manager run CLEAR-COUNTERS !
Output
Router#cc Router# *Apr 27 07:26:39.551: %CLEAR-5-COUNTERS: Clear counter on all interfaces by on vty0 (EEM:CLEAR-COUNTERS)
Note:
+ “cli” here means we will use Command Line Interface (CLI) to type a command
+ “[” and “]” are special characters so we have to put “\” in front of them. “\[” matches “[” and “\]” matches “]”
+ Using the alias command will allow easy execution of the new command. In this example, typing “cc” is equal to “event manager run CLEAR-COUNTERS”.
Example 5
Configure EEM with IP SLA to alert and send a Syslog when a neighbor interface cannot be reached.
We only need a very simple topology with two directly connected routers. On R1 we will track E0/0 interface of R2.
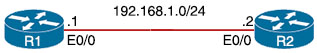
|
R1 int e0/0 |
R2 int e0/0 |
Configure IP SLA on R1:
ip sla 10 icmp-echo 192.168.1.2 timeout 5000 //how long to wait to receive a response (in milliseconds) frequency 10 //how often the test is performed (in seconds) ! ip sla schedule 10 life forever start-time now track 10 ip sla 10 reachability
Configure EEM on R1:
event manager applet EEM_IP_SLA event track 10 state down action 1 syslog msg "Syslog: IP SLA 10 is down" action 2 puts "IP SLA 10 is down!"
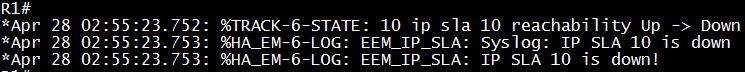
Now we shutdown E0/0 on R2 and we will see this result on R1:
| R2: int e0/0 shutdown |
Output
Summarization
EEM detectors can be:
1) Monitoring SNMP objects
2) Responds to various Syslog messages, allowing for matching on regular expressions
3) Monitoring and responding to interface counter when cross threshold settings
4) Screening CLI input for a regular expression match
5) None: This event detector is use to test EEM script/applet using “event manager run” command
6) Timers: (Countdown, watchdog and CRON)
7) IP SLA and NetFlows events
EEM Actions can be:
1) Sending a email messages
2) Executing a Cisco command
3) Generating SNMP traps
4) Reloading the router
5) Generating prioritized syslog messages
6) Switching to a secondary processor in a redundant platform
7) Requesting system information when an event occurs (like show tech, sh proccess cpu history).



Great! Thx DigitalTut
Very helpful, Thank you
Great! Thanks.
Thanks
very nicely explained, thanks
Great write up. Thanks
Hello, has somebody pass the exam recently?
are these question still valid?
I took the examine and failed. It looks like Cisco changed the questions again. A friend of mine passed it three weeks ago. I utilized his study material and none of the questions where on my examine. I would hold off until your able to locate the new questions.
OMG.Sorry to hear IQ .Now I am worried as well.Planning to take in May or June.Not sure how it is going to be.Thank you IQ for the update.Please keep us informed.Much appreciated
Hi Digitaltut, do we still need to study Encor 350-401? Is it possible to compress all the questions to one link instead of making it per topic?
Thanks!
I just passed my ENCOR exam, many thanks to DigitalTut!! All of the information I’ve seen indicated there would be no labs – however I did get a lab question which I completely failed. Since I still passed I wonder if it was an experimental question. The lab required you to create an EEM script to bring a loopback interface back up if it got shut down.
I am going for 350-401 in 10 days, please do advice what dumps is valid, or these questions here will be enough to study and seat for the test. please do advice
Thank you. Appreciated in advance.
How much is enough to pass 350-401? 87%?
Anyone with valid 350-401 dumps? please assist
thanks
Are these updated ?
Is this site still functioning?
how can i get the valid dump of ENCOR CCNP ?
How can i get the dump of CLCOR CCNP
may I use my account to get ENARSI questions?
How can i get the valid dump of ENCOR CCNP ? anyone to assist???
has anyone seen any labs in the test?
passed the exam yesterday, got 7 labs at the begining, same labs here.
studdied only version 1.1 only and most of the questions here, couple of questions new
Is there any person with vce full send me please to info dot messus at gmail dot com
where is the wireless exam sign in page wirelesstut ?
anyone given ccnp exam recentlty. share your experience
Very nice explaniation about EEM. Finally got it.
is this still the latest dump? planning to take an exam
kaicommon1108@gmail.com