Virtualization Questions
|
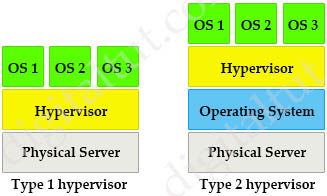
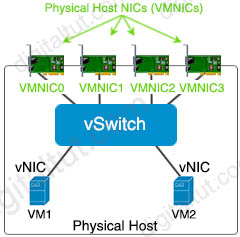
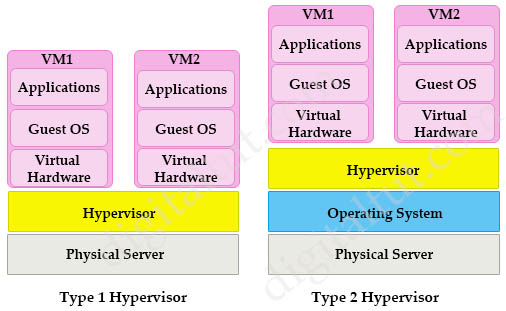
Virtualization Quick Summary A virtual machine (VM) is a software emulation of a physical server with an operating system. From an application’s point of view, the VM provides the look and feel of a real physical server, including all its components, such as CPU, memory, and network interface cards (NICs). A hypervisor, also known as a virtual machine monitor, is a software that creates and manages virtual machines. A hypervisor allows one physical server to support multiple guest VMs by virtually sharing its resources, such as memory and processing. There are two types of hypervisors: type 1 and type 2 hypervisor. In type 1 hypervisor (or native hypervisor), the hypervisor is installed directly on the physical server. Then instances of an operating system (OS) are installed on the hypervisor. Type 1 hypervisor has direct access to the hardware resources. Therefore they are more efficient than hosted architectures. Some examples of type 1 hypervisor are VMware vSphere/ESXi, Oracle VM Server, KVM and Microsoft Hyper-V. In contrast to type 1 hypervisor, a type 2 hypervisor (or hosted hypervisor) runs on top of an operating system and not the physical hardware directly. A big advantage of Type 2 hypervisors is that management console software is not required. Examples of type 2 hypervisor are VMware Workstation (which can run on Windows, Mac and Linux) or Microsoft Virtual PC (only runs on Windows).
Comparison Type 1 and Type 2 hypervisors
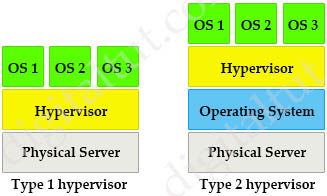
Structure of virtualization in a hypervisor Hypervisors provide virtual switch (vSwitch) that Virtual Machines (VMs) use to communicate with other VMs on the same host. The vSwitch may also be connected to the host’s physical NIC to allow VMs to get layer 2 access to the outside world. Each VM is provided with a virtual NIC (vNIC) that is connected to the virtual switch. Multiple vNICs can connect to a single vSwitch, allowing VMs on a physical host to communicate with one another at layer 2 without having to go out to a physical switch.
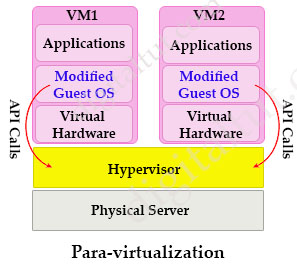
Although vSwitch does not run Spanning-tree protocol but vSwitch implements other loop prevention mechanisms. For example, a frame that enters from one VMNIC is not going to go out of the physical host from a different VMNIC card. Benefits of Virtualizing Server virtualization and the use of virtual machines is profoundly changing data center dynamics. Most organizations are struggling with the cost and complexity of hosting multiple physical servers in their data centers. The expansion of the data center, a result of both scale-out server architectures and traditional “one application, one server” sprawl, has created problems in housing, powering, and cooling large numbers of underutilized servers. In addition, IT organizations continue to deal with the traditional cost and operational challenges of matching server resources to organizational needs that seem fickle and ever changing. Virtual machines can significantly mitigate many of these challenges by enabling multiple application and operating system environments to be hosted on a single physical server while maintaining complete isolation between the guest operating systems and their respective applications. Hence, server virtualization facilitates server consolidation by enabling organizations to exchange a number of underutilized servers for a single highly utilized server running multiple virtual machines. By consolidating multiple physical servers, organizations can gain several benefits: Para-virtualization Para-virtualization is an enhancement of virtualization technology in which a guest operating system (guest OS) is modified prior to installation inside a virtual machine. This allows all guest OS within the system to share resources and successfully collaborate, rather than attempt to emulate an entire hardware environment. The modification also decreases the execution time required to complete operations that can be problematic in virtual environments.
By granting the guest OS access to the underlying hardware, Para-virtualization enables communication between the guest OS and the hypervisor (using API calls), thus improving performance and efficiency within the system. This is the main difference between Para-virtualization and (traditional) full-virtualization. |
Question 1
Explanation
There is nothing special with the configuration of Gi0/0 on R1. Only Gi0/0 interface on R2 is assigned to VRF VPN_A. The default VRF here is similar to the global routing table concept in Cisco IOS
Question 2
Explanation
Answer C and answer D are not correct as only route distinguisher (RD) identifies the customer routing table and “allows customers to be assigned overlapping addresses”.
Answer A is not correct as “When BGP is configured, route targets are transmitted as BGP extended communities”
Question 3
Explanation
In VRF-Lite, Route distinguisher (RD) identifies the customer routing table and allows customers to be assigned overlapping addresses. Therefore it can support multiple customers with overlapping addresses -> Answer E is correct.
VRFs are commonly used for MPLS deployments, when we use VRFs without MPLS then we call it VRF lite -> Answer C is not correct.
– VRF-lite does not support IGRP and ISIS. ( -> Answer B is not correct)
– The capability vrf-lite subcommand under router ospf should be used when configuring OSPF as the routing protocol between the PE and the CE.
– VRF-lite does not affect the packet switching rate. (-> Answer A is not correct)
Question 4
Explanation
There are two types of hypervisors: type 1 and type 2 hypervisor.
In type 1 hypervisor (or native hypervisor), the hypervisor is installed directly on the physical server. Then instances of an operating system (OS) are installed on the hypervisor. Type 1 hypervisor has direct access to the hardware resources. Therefore they are more efficient than hosted architectures. Some examples of type 1 hypervisor are VMware vSphere/ESXi, Oracle VM Server, KVM and Microsoft Hyper-V.
In contrast to type 1 hypervisor, a type 2 hypervisor (or hosted hypervisor) runs on top of an operating system and not the physical hardware directly. A big advantage of Type 2 hypervisors is that management console software is not required. Examples of type 2 hypervisor are VMware Workstation (which can run on Windows, Mac and Linux) or Microsoft Virtual PC (only runs on Windows).
Question 5
Explanation
Server virtualization and the use of virtual machines is profoundly changing data center dynamics. Most organizations are struggling with the cost and complexity of hosting multiple physical servers in their data centers. The expansion of the data center, a result of both scale-out server architectures and traditional “one application, one server” sprawl, has created problems in housing, powering, and cooling large numbers of underutilized servers. In addition, IT organizations continue to deal with the traditional cost and operational challenges of matching server resources to organizational needs that seem fickle and ever changing.
Virtual machines can significantly mitigate many of these challenges by enabling multiple application and operating system environments to be hosted on a single physical server while maintaining complete isolation between the guest operating systems and their respective applications. Hence, server virtualization facilitates server consolidation by enabling organizations to exchange a number of underutilized servers for a single highly utilized server running multiple virtual machines.
By consolidating multiple physical servers, organizations can gain several benefits:
+ Underutilized servers can be retired or redeployed.
+ Rack space can be reclaimed.
+ Power and cooling loads can be reduced.
+ New virtual servers can be rapidly deployed.
+ CapEx (higher utilization means fewer servers need to be purchased) and OpEx (few servers means a simpler environment and lower maintenance costs) can be reduced.
Question 6
Explanation
A virtual machine (VM) is a software emulation of a physical server with an operating system. From an application’s point of view, the VM provides the look
and feel of a real physical server, including all its components, such as CPU, memory, and network interface cards (NICs).
The virtualization software that creates VMs and performs the hardware abstraction that allows multiple VMs to run concurrently is known as a hypervisor.
There are two types of hypervisors: type 1 and type 2 hypervisor.
In type 1 hypervisor (or native hypervisor), the hypervisor is installed directly on the physical server. Then instances of an operating system (OS) are installed on the hypervisor. Type 1 hypervisor has direct access to the hardware resources. Therefore they are more efficient than hosted architectures. Some examples of type 1 hypervisor are VMware vSphere/ESXi, Oracle VM Server, KVM and Microsoft Hyper-V.
In contrast to type 1 hypervisor, a type 2 hypervisor (or hosted hypervisor) runs on top of an operating system and not the physical hardware directly. A big advantage of Type 2 hypervisors is that management console software is not required. Examples of type 2 hypervisor are VMware Workstation (which can run on Windows, Mac and Linux) or Microsoft Virtual PC (only runs on Windows).
Question 7
Question 8
Explanation
Because some PE routers might receive routing information they do not require, a basic requirement is to be able to filter the MP-iBGP updates at the ingress to the PE router so that the router does not need to keep this information in memory.
The Automatic Route Filtering feature fulfills this filtering requirement. This feature is available by default on all PE routers, and no additional configuration is necessary to enable it. Its function is to filter automatically VPN-IPv4 routes that contain a route target extended community that does not match any of the PE’s configured VRFs. This effectively discards any unwanted VPN-IPv4 routes silently, thus reducing the amount of information that the PE has to store in memory -> Answer D is correct.
Reference: MPLS and VPN Architectures Book, Volume 1
The reason that PE1 dropped the route is there is no “route-target import 999:999” command on PE1 (so we see the “DENIED due to:extended community not supported” in the debug) so we need to type this command to accept this route -> Answer E is correct.
Question 9
Explanation
Broadcast radiation refers to the processing that is required every time a broadcast is received on a host. Although IP is very efficient from a broadcast perspective when compared to traditional protocols such as Novell Internetwork Packet Exchange (IPX) Service Advertising Protocol (SAP), virtual machines and the vswitch implementation require special consideration. Because the vswitch is software based, as broadcasts are received the vswitch must interrupt the server CPU to change contexts to enable the vswitch to process the packet. After the vswitch has determined that the packet is a broadcast, it copies the packet to all the VMNICs, which then pass the broadcast packet up the stack to process. This processing overhead can have a tangible effect on overall server performance if a single domain is hosting a large number of virtual machines.
Note: This overhead effect is not a limitation of the vswitch implementation. It is a result of the software-based nature of the vswitch embedded in the ESX hypervisor.
—————————————————————-
Note about the structure of virtualization in a hypervisor:
Hypervisors provide virtual switch (vSwitch) that Virtual Machines (VMs) use to communicate with other VMs on the same host. The vSwitch may also be connected to the host’s physical NIC to allow VMs to get layer 2 access to the outside world.
Each VM is provided with a virtual NIC (vNIC) that is connected to the virtual switch. Multiple vNICs can connect to a single vSwitch, allowing VMs on a physical host to communicate with one another at layer 2 without having to go out to a physical switch.
Although vSwitch does not run Spanning-tree protocol but vSwitch implements other loop prevention mechanisms. For example, a frame that enters from one VMNIC is not going to go out of the physical host from a different VMNIC card.
Question 10
Explanation
A bare-metal hypervisor (Type 1) is a layer of software we install directly on top of a physical server and its underlying hardware. There is no software or any operating system in between, hence the name bare-metal hypervisor. A Type 1 hypervisor is proven in providing excellent performance and stability since it does not run inside Windows or any other operating system. These are the most common type 1 hypervisors:
+ VMware vSphere with ESX/ESXi
+ KVM (Kernel-Based Virtual Machine)
+ Microsoft Hyper-V
+ Oracle VM
+ Citrix Hypervisor (formerly known as Xen Server)



Are this questions in the current exam?
@digitaltut Hello, please add Q8 on the quizzes thank you
@digitaltut I think you need to update other questions on the quizzes some are not available in the quizzes and there are some questions on the quizzes are not on the site. thanks.
@jlai: We have just optimized some topics (Virtualization, Miscellaneous and LISP VXLAN Questions) so some of the questions have been swapped. We have just updated all of them so please try again!
question number 1 , is the answer not A ??
Question 3
Which two statements about VRF-lite are true? (Choose two)
A. It can increase the packet switching rate
B. It supports most routing protocols, including EIGRP, ISIS, and OSPF
C. It supports MPLS-VRF label exchange and labeled packets
D. It should be used when a customer’s router is connected to an ISP over OSPF
E. It can support multiple customers on a single switch
Answer is D and E
Reference: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst4500/12-2/25ew/configuration/guide/conf/vrf.html#wp1045190
@digitaltut
Question 3
Answer is D and E
– VRF-lite does not support IGRP and ISIS.
– The capability vrf-lite subcommand under router ospf should be used when configuring OSPF as the routing protocol between the PE and the CE.
Reference: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst4500/12-2/25ew/configuration/guide/conf/vrf.html#wp1045190
@Heamgu, @OniWAbaN: Thanks for your detection, we have just updated Q.3.
@digitaltut Question 3 in Quiz doesn’t update.
@digitaltut Question 3 in Quiz doesn’t update.
Question 1 : A on avis c’est plutôt D.
Hello, there are different answers in dumps:
What are two reasons why broadcast radiation is caused in the virtual machine environment?
(Choose two)
A. vSwitch must interrupt the server CPU to process the broadcast packet
B. The Layer 2 domain can be large in virtual machine environments
C. Virtual machines communicate primarily through broadcast mode
D. Communication between vSwitch and network switch is broadcast based
E. Communication between vSwitch and network switch is multicast based
Which two are the correct ones?
Regards.
I believe the answer should be A&D
Can someone confirm what is correct answer?
What are two reasons why broadcast radiation is caused in the virtual machine environment? (Choose two)
A. vSwitch must interrupt the server CPU to process the broadcast packet
B. The Layer 2 domain can be large in virtual machine environments
C. Virtual machines communicate primarily through broadcast mode
D. Communication between vSwitch and network switch is broadcast based
E. Communication between vSwitch and network switch is multicast based
Answer: A C or A D?
Question 3
Which two statements about VRF-lite are true? (Choose two)
A. It can increase the packet switching rate
B. It supports most routing protocols, including EIGRP, ISIS, and OSPF
C. It supports MPLS-VRF label exchange and labeled packets
D. It should be used when a customer‘s router is connected to an ISP over OSPF
E. It can support multiple customers on a single switch
I believe the answer should be B, E
@As
VRF-lite does not support IGRP and ISIS. You can find the answer in this link:
https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst4500/12-2/25ew/configuration/guide/conf/vrf.html#wp1045190
@AS
So B would not have been the answer. The correct options are D & E.
For this:
What are two reasons why broadcast radiation is caused in the virtual machine environment? (Choose two)
A. vSwitch must interrupt the server CPU to process the broadcast packet
B. The Layer 2 domain can be large in virtual machine environments
C. Virtual machines communicate primarily through broadcast mode
D. Communication between vSwitch and network switch is broadcast based
E. Communication between vSwitch and network switch is multicast based
Answer is: A & B.
Source:
Because the vswitch is software based, as broadcasts are received the vswitch must interrupt the server CPU to change contexts to enable the vswitch to process the packet. After the vswitch has determined that the packet is a broadcast, it copies the packet to all the VMNICs, which then pass the broadcast packet up the stack to process. This processing overhead can have a tangible effect on overall server performance if a single domain is hosting a large number of virtual machines.
https://www.cisco.com/c/en/us/solutions/collateral/data-center-virtualization/net_implementation_white_paper0900aecd806a9c05.html
@Joker is asking the causes. B D for me
*B C
NO.11 what is a benefit of using a Type 2 hypervisor instead of a Type 1 hypervisor?
A. better application performance
B. Improved security because the underlying OS is eliminated
C. Improved density and scalability
D. ability to operate on hardware that is running other OSs
please what is the correct answer of this question ?
NO.11 what is a benefit of using a Type 2 hypervisor instead of a Type 1 hypervisor?
A. better application performance
B. Improved security because the underlying OS is eliminated
C. Improved density and scalability
D. ability to operate on hardware that is running other OSs
no. 11 answer should be D
ADMIN………………………. please check Q 9 .. the answer should be A and C ….????
levitra length of effect https://uslevitraanna.com/ price for levitra
Hi Admin,
Can you confirm the answers.
Regards
Hi Admin,
Can you confirm the answers of Q9
Regards
Hello! How can I get to your office?
@digitaltut; please provide summary of VRF Lite also.
Question 3
This link shows how to configure VRF-Lite with EIGRP:
https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst4500/XE3-6-0E/15-22E/configuration/guide/xe-360-config/vrf.html
Isn’t the one you provided specific to 4500?
@Damien,
Yes, that is correct. the reference they are using her IOS 12.
We are in the age of IOS XE, where as you mentioned all Routing Protocols support VRF lite.
I would go with B and E.
Hoping that the exam writter in is age of IOS XE(17), not IOS 12
@Ytake
I would say the same. but…
@digitaltut : Do we have to answer as current cpabilities IOS XE or old IOS ?
Q3:
EIGRP is asked (not IGRP) – both EIGRP and IS-IS are supported in VRF lite:
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/iproute_isis/configuration/xe-16/irs-xe-16-book/irs-instance-vrf.html
Q3 answer E is crap. What on earth they say switch in the end?